The Science of Cyber Risk Propagation & Financial Impact
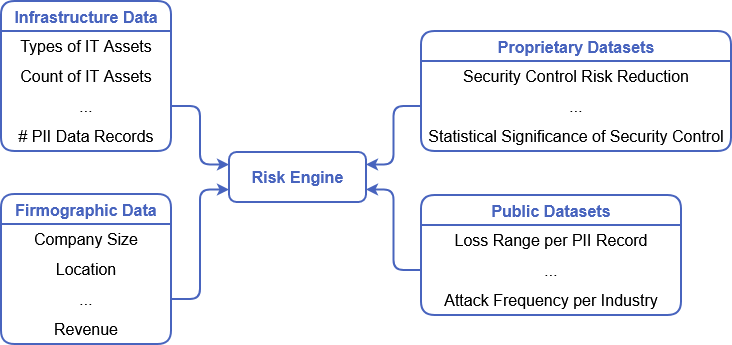
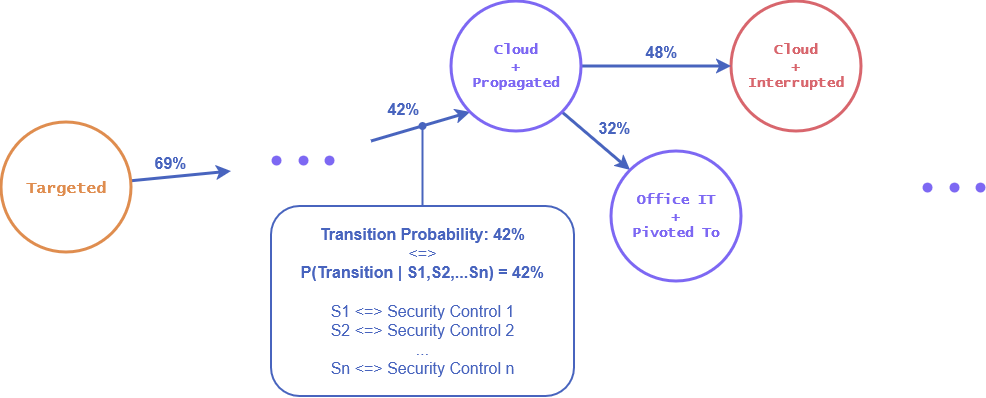
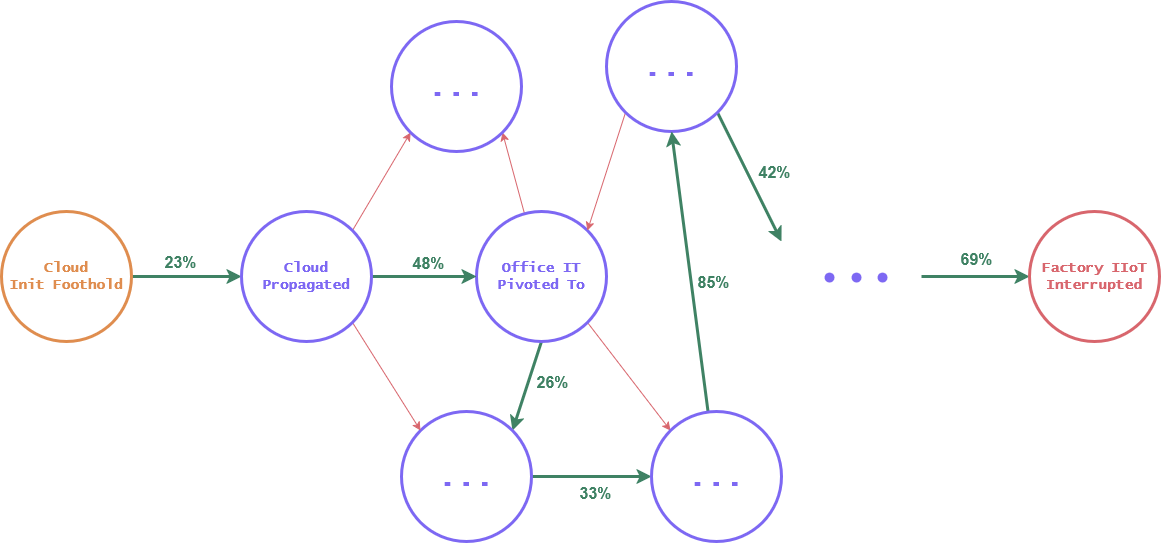
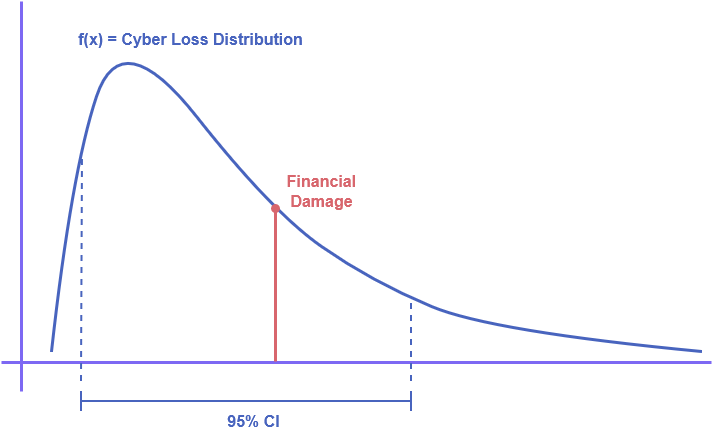
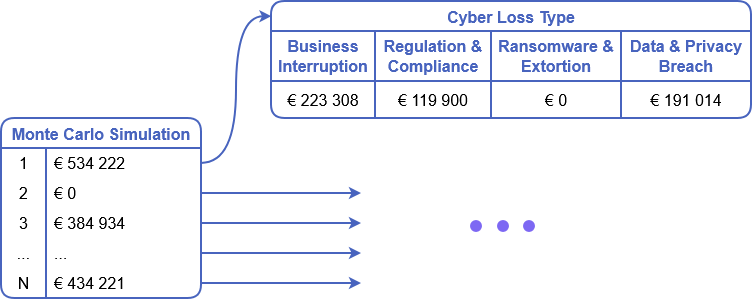
Understand how our algorithm works to move beyond static scoring. Arakt uses stochastic modeling and advanced attack-path simulations to map how cyber risk cascades through your infrastructure, quantifying your exposure with actuarial precision.
Get Started